When it comes to securing your organization's digital assets, penetration testing is one of the most powerful tools in a cybersecurity professional's arsenal. But one question consistently divides security teams: should you prioritize internal or external penetration testing? The short answer is that both matter - but understanding the key differences, use cases, and strategic value of each is essential for building a robust security posture.
At PIT Solutions, our cybersecurity team works with organizations across industries to deliver continuous vulnerability assessments and managed SOC services that go far beyond a one-time test. In this blog, we break down internal vs. external pen testing - so you can make an informed decision about what your business truly needs.
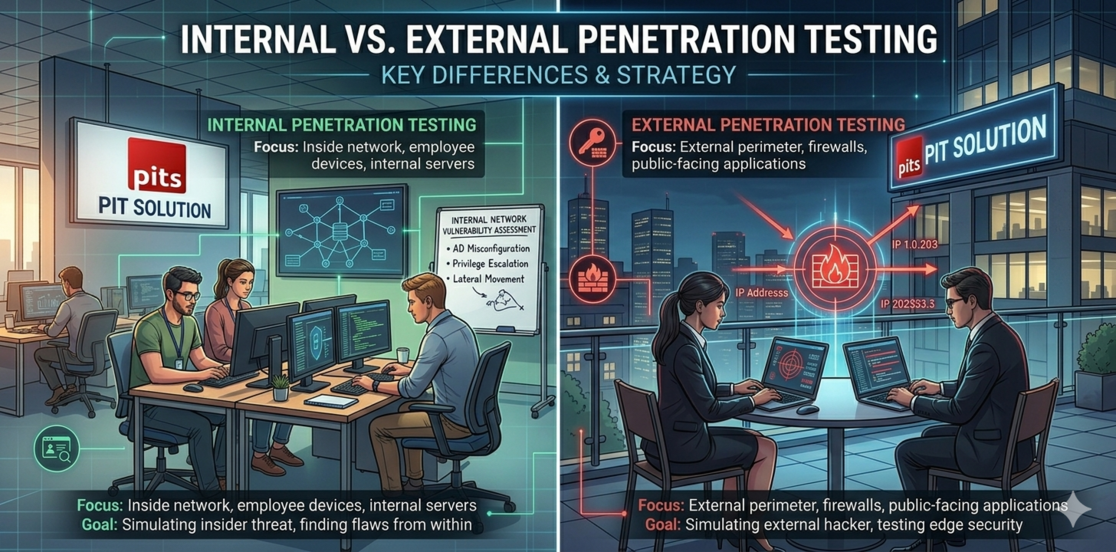
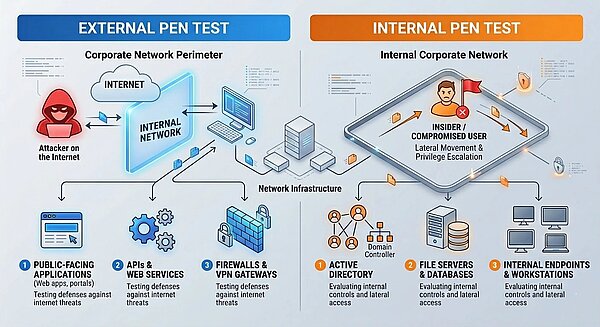
What Is External Penetration Testing?
External penetration testing puts you in the shoes of a real attacker, trying to break into your organization from the outside-no inside help, just what’s out there for anyone to find. Testers poke at everything that faces the internet: public websites, APIs, your firewalls and routers, email security, VPNs, remote desktop, DNS, cloud stuff, any storage that’s not locked down. The whole point is finding the weak spots before someone else does. If an attacker can slip in through one of these exposed doors, they can reach your systems, steal data, or move deeper into the network. IBM’s 2023 Cost of a Data Breach Report spells it out: the average breach costs $4.45 million, and a lot of attacks start with something left open to the internet. Catching these gaps with external testing lets you fix them before they become expensive problems.
What Is Internal Penetration Testing?
Internal penetration testing simulates an attack from within your network - mimicking the actions of a malicious insider, a compromised employee account, or an attacker who has already bypassed perimeter defenses. The tester is given (or obtains) access to the internal network and attempts to:
-
Escalate privileges to gain administrative or root access
-
Move laterally across the network to access sensitive systems
-
Exfiltrate sensitive data such as customer records or intellectual property
-
Compromise Active Directory, internal databases, or file servers
-
Abuse misconfigured services, shares, and internal applications
The Goal: Determine how much damage a rogue insider or a post-breach attacker could cause, and identify internal gaps in detection, segmentation, and access controls.
Internal vs External Penetration Testing: Key Differences
| Factor | External Pen Test | Internal Pen Test |
| Attack Vector | Outside the organization | Inside the organization |
| Simulates | External hackers / APTs | Insiders / post-breach attackers |
| Targets | Internet-facing assets | Internal systems & data |
| Primary Risk | Perimeter vulnerabilities | Lateral movement & privilege escalation |
| Compliance Use | PCI-DSS, ISO 27001, SOC 2 | HIPPA, GDPR, ISO 27001 |
| Frequency | Annually or after major changes | Annually or after incidents |
| Complexity | Moderate to High | High |
Which One Matters More?
The honest answer: neither one matters more in isolation - they address fundamentally different threat scenarios. The right question isn't "which is better" but rather "which does my organization need right now, and how do they work together?"
When Should You Choose External Pen Testing?
- You've recently launched a new web application or API
- Your organization has significant internet-facing infrastructure
- You're pursuing compliance certifications (PCI-DSS, SOC 2, ISO 27001)
- You've never conducted a security assessment before
- You've experienced a recent external-origin breach or incident
When Should You Choose Internal Pen Testing?
- You handle sensitive customer or financial data (healthcare, finance, legal)
- Your organization has many privileged user accounts or complex AD environments
- You're concerned about insider threat risks
- You've recently experienced a breach that bypassed perimeter defenses
- You need to validate your network segmentation and zero-trust architecture
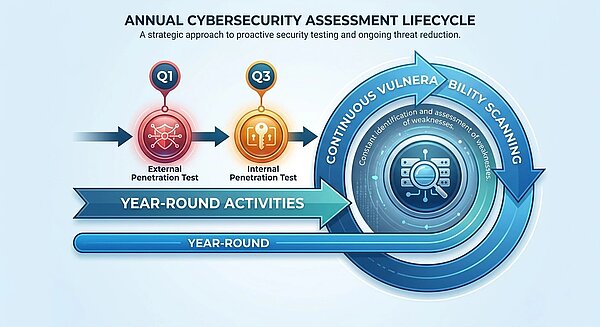
Why a Combined Pen Testing Strategy Works Best
The most resilient organizations don't choose between internal and external pen testing — they implement both as part of a continuous security testing program. This layered approach provides a complete picture of your threat landscape.
At PIT Solutions, we advocate for a risk-based testing framework that considers your industry, threat profile, compliance requirements, and budget. Our certified security professionals leverage industry-standard frameworks including OWASP, NIST, and CIS Controls to ensure comprehensive coverage across your entire attack surface.
A combined annual testing cycle may include: an external pen test in Q1 to assess perimeter defenses after year-end changes, an internal pen test in Q3 to validate internal controls, and continuous vulnerability scanning year-round to catch newly disclosed CVEs before attackers do. To learn more about how a fully managed approach can complement your testing program, explore Managed Cybersecurity Services for business protection by PIT Solutions.
Compliance & Regulatory Considerations
Regulatory frameworks increasingly mandate regular penetration testing. Understanding which type of testing maps to your compliance requirements can help justify the investment:
- PCI-DSS v4.0 – Requires both external and internal pen testing annually, and after significant infrastructure changes.
- HIPAA – Mandates security risk assessments; internal pen testing is critical for protecting PHI from insider threats.
- ISO/IEC 27001 – Calls for regular security testing as part of an Information Security Management System (ISMS).
- SOC 2 Type II – Requires evidence of ongoing vulnerability management, often satisfied by regular pen tests.
-
GDPR – While not prescriptive on methodology, regular testing demonstrates due diligence for data protection.
How PIT Solutions Strengthens Your Security
While penetration testing is a valuable point-in-time assessment, the reality is that threats don’t operate on an annual schedule. New vulnerabilities are disclosed daily, attackers evolve their tactics continuously, and a single unpatched system can become the entry point for a major breach. This is why PIT Solutions goes beyond one-time assessments, offering continuous Vulnerability Assessment and Security Operations Center (SOC) services that keep your organization protected 24/7 - not just once a year. As part of our Managed IT and Cyber Security Services, we deliver a layered, always-on security model that includes:
- Continuous Vulnerability Assessment: Ongoing scanning and identification of vulnerabilities across your internal and external attack surface, ensuring newly disclosed CVEs are detected before they can be exploited.
- 24/7 SOC Monitoring: Round-the-clock threat detection, log analysis, and incident response by a dedicated Security Operations Center team — because breaches don’t wait for business hours.
- Threat Intelligence & Prioritization: Risk-based vulnerability prioritization using real-world threat intelligence, so our team focuses remediation efforts where it matters most.
- Incident Detection & Response: Rapid identification and containment of security incidents, minimizing dwell time and limiting the blast radius of any breach attempt.
- Compliance Reporting & Dashboards: Continuous evidence collection and reporting to support PCI-DSS, HIPAA, ISO 27001, and SOC 2 compliance requirements — without the last-minute scramble before an audit.
The difference between a one-time pen test and a continuous security program is the difference between a snapshot and a live feed. With PIT Solutions, your security posture is monitored, measured, and improved every single day - giving your security and executive teams real-time visibility into risk, not just an annual report.
Final Verdict: It's Not Either/Or
Internal and external penetration testing are not competing methodologies - they're complementary layers of a mature security program. External testing tells you how hard it is for an attacker to get in. Internal testing tells you how much damage they could do once inside. You need both answers to truly understand your risk.
Security-conscious organizations don't ask "which test do I need?" - they ask, "how do I build a testing program that continuously validates our defenses against evolving threats?" The answer lies in combining the insights from vulnerability assessments with the always-on protection of a managed SOC. That mindset, combined with the right partner, is what separates organizations that react to breaches from those that prevent them.
Partner with PIT Solutions to build a security strategy that’s as dynamic as the threats you face - with continuous vulnerability assessment and round-the-clock SOC monitoring at its core. Because in cybersecurity, the question was never internal vs. external - it's always been tested vs. untested.