What are ransomware attacks and why are they becoming one of the most disruptive forms of modern cybercrime? Ransomware is a type of malware attack used for cyber extortion, where attackers encrypt data or steal critical files and demand payment for recovery. With ransomware now linked to a growing share of data breaches, understanding how these attacks begin, how they move through the ransomware lifecycle and steps that can prevent data encryption is essential. This guide answers what ransomware attacks are and outlines practical ways to stop ransomware before high impact damage occurs.
What Is Ransomware? (Modern Definition & How It Has Evolved)
Ransomware is a form of cyber extortion that uses file encryption malware to lock data and demand payment. It is a malicious campaign designed to disrupt systems, steal information and pressure victims into paying for recovery. While traditional ransomware focused only on encryption, modern attacks often include data theft and double or triple extortion threats. The rise of the ransomware service model, supported by dark web markets and affiliate programs, has made ransomware evolution faster and more scalable worldwide.
Why Ransomware Attacks Are Increasing Worldwide
Ransomware attacks are rising rapidly due to changing ransomware trends and the growing profitability of cybercrime. RaaS business models enable attackers to scale their operations on an affiliate profit sharing basis, and cryptocurrency provides a means of anonymous crypto ransom payments. There are also new digital transformation risks presented by remote work and cloud adoption that enlarge the malware campaign attack surface. Moreover, the use of supply chain attacks and third party compromises offers threat actors greater access with limited effort making ransomware a low risk, high reward type of cybercrime development in the global community.
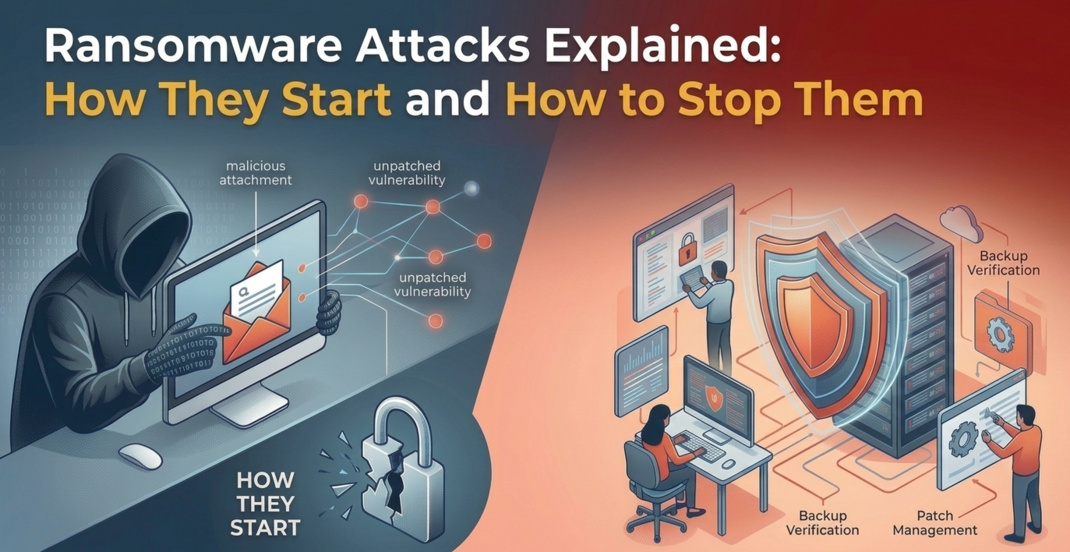
How Ransomware Attacks Start (Initial Access Methods)
Most ransomware attacks start through common entry points that attackers use to gain access to networks. By understanding these initial access methods, organizations can reduce exposure and stop ransomware early.
- Phishing Emails: Malicious links or attachments entice users to open the door to ransomware.
- Remote Access Compromise (RDP): Attackers can use weak or stolen credentials to get into systems remotely.
- Software Vulnerabilities: Applications and old systems that are not patched are easy to access.
- Drive by Downloads/Bad Websites: Malware downloads can occur just by accessing a malicious site.
- Malvertising: Online fake ads contain malicious code that is concealed.
- Infected Removable Media: USB drives and external devices have the ability to propagate ransomware to networks.
The Full Ransomware Attack Lifecycle (From Entry to Extortion)
Ransomware attacks typically follow a step by step ransomware kill chain:
- Initial compromise: Attackers gain entry through phishing, RDP abuse or software vulnerabilities.
- Persistence and lateral movement: Malware spreads across systems to maintain access.
- Privilege escalation: Higher level permissions are obtained to control critical assets.
- Data discovery and exfiltration: Sensitive data is identified and sent to remote hacker servers.
- Encryption execution: Files and systems are encrypted to disrupt operations.
- Ransom note delivery and extortion: Attackers demand payment and threaten data exposure.
What Happens After Infection? (Encryption, Threats & Pressure Tactics)
After unauthorized access, ransomware activates encryption mechanisms and key management to lock critical files using advanced encryption algorithms. Attackers often perform shadow copy deletion and remove backups to prevent recovery. Many groups then use data leak sites, public disclosure threats and DDoS extortion to increase pressure during ransom negotiations. In triple extortion cases, customers and partners may also be targeted to force faster payment. This is a key part of ransomware explained, showing how attacks escalate beyond encryption into aggressive extortion tactics.
Types of Ransomware Attacks
There are various types of ransomware attacks and each of them is meant to disrupt systems or put pressure on victims in a certain manner. Some types lock or encrypt data, while others focus on stealing information and threatening its exposure.
-
Crypto Ransomware
This type encrypts files and makes them unusable until a ransom is paid. Crypto lockers are the most common form of ransomware today.
-
Locker Ransomware
Locker ransomware blocks access to the entire device or system instead of individual files. Victims cannot use their computer until the ransom demand is addressed.
-
Double Extortion Ransomware
Attackers encrypt data and also steal sensitive information. They threaten to publish the stolen data if the ransom is not paid.
-
Triple Extortion Ransomware
This model adds extra pressure by targeting customers, partners or launching additional attacks like DDoS. It increases urgency and financial impact.
-
Wipers
Wipers are destructive malware designed to erase or permanently damage data. Even if payment is made, recovery may not be possible.
-
Doxware
Doxware focuses on stealing personal or confidential data and threatening public release. The goal is reputational harm rather than encryption alone.
-
Ransomware Worms
These ransomware worms spread automatically across networks without user action. They can infect large environments quickly.
-
Extortion-Only Malware
In these attacks, data is stolen but not encrypted. Criminals demand payment purely to prevent public exposure or misuse of the stolen information.
Most Notorious and Active Ransomware Families
Ransomware by industry shows that attackers focus on sectors where disruption causes urgent pressure to pay. From hospital ransomware cases to supply chain ransomware campaigns, threat actors target organizations that rely on continuous operations and sensitive data.
- Healthcare and life sciences: Hospitals and clinics are frequent targets because patient care depends on system access.
- Government and municipalities: Municipal cyberattacks can disrupt public services and critical records.
- Education and research institutions: Universities often face attacks due to large networks and valuable research data.
- Manufacturing and critical infrastructure: Shutdowns in production or utilities create major financial and safety risks.
- Financial services: Banks and insurers are targeted for high value data and direct monetary impact.
- MSPs and supply chain providers: Attackers use these organizations to reach multiple clients through one breach.
- SMBs vs enterprises: Both are attacked, SMBs often lack defenses, while enterprises offer larger payouts.
The Business Impact of Ransomware Attacks
Ransomware attacks cause extreme business interruption, including financial, operational, and long-term reputational damage. The total ransomware payments usually involve business disruption, regulatory liability and reputational risk that may extend far beyond the occurrence of the original event.
- Financial losses and recovery costs: This covers ransom fees, system recovery and reaction services.
- Operational downtime and service disruption: Attacks can disrupt the operation of the business and delay essential services.
- Data loss and corruption: Encrypted or stolen data may be permanently damaged or unrecoverable.
- Legal, regulatory and compliance penalties: Organizations may face regulatory fines and data breach penalties.
- Brand reputation damage: Public incidents can weaken market credibility and brand value.
- Customer trust erosion: Clients may lose confidence in the organization’s ability to protect data.
- Cyber insurance implications: Coverage disputes and higher premiums can follow cyber insurance claims.
Should You Pay the Ransom? (Risks, Ethics & Legal Reality)
Paying a ransom may seem like a quick way to recover, but it carries major legal, ethical and security risks. There is no guarantee attackers will restore access, and payment can increase the chance of repeat ransomware attacks. Law enforcement advice and regulations including OFAC sanctions, often discourage funding cybercrime through ransom payments.
- Arguments for and against paying: Payment may seem like a fast solution, but it can also increase long term risk.
- Legal and regulatory issues: Ransom payments can be illegal or can lead to the imposition of OFAC sanctions.
- Repeat targeting risk: Paying organizations are usually re-targeted by the same or other threat actors.
- Government advice and law enforcement: The advice of the government in most cases is to contain and recover rather than to pay.
- Cybercrime funding implications: Financing aids criminal gangs and encourages further assaults.
How to Stop Ransomware Attacks (Prevention Framework)
A layered security strategy is needed to prevent ransomware by minimizing the attacker's entry points. By applying proven cybersecurity best practices, organizations can strengthen defenses and lower the risk of disruption. If you want to know how to stop ransomware attacks, here are some best practices.
- Security awareness and phishing training: Helps employees recognize and avoid malicious emails.
- Patch management and vulnerability remediation: Closes security gaps attackers exploit.
- Multi factor authentication (MFA): Adds protection even if passwords are stolen.
- Endpoint detection and response (EDR/XDR): Detects and responds to ransomware activity early.
- Email security and DNS filtering: Blocks harmful links, attachments and domains.
- Network segmentation: Prevents ransomware from spreading across systems.
- Zero Trust architecture: Requires continuous verification for every user and device.
- Least privilege access controls: Limits access to only what is necessary, reducing impact.
The Role of Backups in Ransomware Defense
Backups are one of the most reliable defenses against ransomware because they support fast data restoration without paying attackers. A strong ransomware backup strategy also strengthens disaster recovery and business continuity planning.
- 3-2-1 backup strategy: Keep three copies of data on two different storage types, with one stored offsite.
- Offline and immutable backups: Prevent attackers from deleting or encrypting backup files.
- Backup testing and restoration drills: Ensure backups actually work during real incidents.
Cloud vs on-prem backup security: Both require strong access controls and protection against compromise.
How to Detect Ransomware Early
Early ransomware detection helps stop attacks before encryption spreads across systems. Monitoring suspicious activity and using security telemetry improves response speed.
- Behavioral indicators and anomaly detection: Identify unusual system behavior linked to ransomware.
- File system monitoring: Detects rapid file changes or encryption patterns.
- Network traffic analysis: Spot abnormal connections or data transfers.
- Threat intelligence feeds: Stay updated on known ransomware tactics and actors.
- Indicators of compromise (IOCs): Track malicious files, domains and signatures.
What to Do If You’re Hit by Ransomware (Step-by-Step Response Guide)
A clear ransomware incident response plan reduces damage and speeds recovery. Immediate containment and professional support are critical.
- Immediate containment steps: Act quickly to stop further spread.
- Isolating infected systems: Disconnect affected devices from the network.
- Preserving forensic evidence: Support digital forensics and investigation.
- Notifying stakeholders: Inform leadership, IT teams and key partners.
- Engaging cybersecurity professionals: Get expert support for containment and recovery.
- Reporting to authorities: Follow law enforcement reporting guidance.
- Restoring from backups: Recover systems safely after cleanup.
Post-incident review: Improve defenses based on lessons learned.
Legal, Compliance and Regulatory Considerations
Ransomware compliance involves legal reporting obligations, industry standards and regulatory penalties. Organizations must understand their responsibilities after an attack.
- Data breach notification laws: Required reporting timelines vary by region.
- Industry compliance standards: HIPAA, GDPR and PCI DSS may apply.
- Sanctions risks and OFAC guidance: Ransom payments may violate sanctions rules.
- Cyber insurance policies and exclusions: Coverage depends on policy terms and response actions.
The Future of Ransomware (Trends, Tactics & Predictions)
Ransomware trends in 2025 and beyond include faster, smarter, and more automated attackers.The emerging cyber threats will need more robust prevention and adaptive security measures.
- AI-powered ransomware: AI will improve targeting and attack efficiency.
- Automated exploitation and reconnaissance: Faster scanning and intrusion methods will grow.
- Increased supply chain targeting: Attackers will use third parties to reach larger networks.
- Extortion without encryption: Data theft alone may replace encryption in some attacks.
- Law enforcement and regulatory evolution: Governments will expand cybercrime enforcement and compliance demands.
Key Takeaways & Ransomware Defense Checklist
Ransomware defense requires more than basic security tools. To understand what is ransomware, it is a form of cyber extortion that encrypts or steals data and demands payment for recovery, making prevention essential. Organizations need a clear ransomware defense checklist, strong cybersecurity maturity and an active risk management framework. Key priorities for cybersecurity include phishing awareness, timely software patching, multifactor authentication (MFA) and endpoint protection. Organizations should also avoid common pitfalls such as weak access controls and untested updates or backups. Additionally, ransomware defense requires maintaining secure recovery plans, ongoing monitoring and a proactive improvement approach due to the changing nature of threats. Partnering with an experienced IT solutions company like PIT Solutions, a trusted cybersecurity company, helps businesses strengthen long term cyber resilience and implement scalable ransomware protection strategies.