Today's businesses operate in a world without the conventional network perimeter. Business ecosystems rely heavily on third-party integrations, employees work remotely, and apps operate in multi-cloud environments.
Organizations now need to approach security in a completely different way due to this change.
Cyber threats now directly affect business continuity, regulatory compliance, customer trust, and revenue growth; they are no longer isolated technical problems. Because of this, businesses in all sectors are adopting Zero Trust Architecture (ZTA) as a fundamental cybersecurity framework for modern enterprises. At PIT Solutions, we help organizations across industries design and implement robust Zero Trust strategies tailored to their unique security needs.
What is Zero Trust Architecture?
Zero Trust Architecture is built on the principle:
“Never trust, always verify.”
It makes sure that every user, device and application is always checked and approved before they can use resources. This gets rid of the idea that networks are always safe.
Zero Trust is different, from security models. It works well for businesses that are spread out. It is not focused on an industry.
Why Zero Trust Matters for Modern Enterprises
Regardless of sector, every organization today faces three common challenges:
- Increasing digital exposure
- Rising cyber threats
- Growing regulatory pressure
Zero Trust addresses these challenges by creating a consistent, scalable, and business-aligned security framework. Explore how PIT Solutions’ cybersecurity services help enterprises address these exact challenges with a Zero Trust implementation strategy.
Industry Use Cases of Zero Trust Architecture

Banking & Financial Services
In banking and financial services, the stakes couldn't be higher every transaction carries risk, and customer data is always a target. That's where Zero Trust comes in. Rather than assuming anyone inside the network can be trusted, it insists on verifying every user, every time. This makes it significantly harder for fraudsters or rogue insiders to slip through the cracks, even when they've managed to steal legitimate credentials.
Beyond security, Zero Trust also makes life easier when regulators come knocking. Because every access point is logged and controlled, organisations are always audit-ready no scrambling to piece together who accessed what and when.
Retail & E-commerce
Retail businesses are over the place these days. You can find them in physical stores on websites on apps in warehouses and everywhere in between. This is really good for reaching customers. It also means that people who want to do bad things on the internet have a lot of ways to get in.
Zero Trust is a way to stop these people from getting in. It makes sure that every time someone buys something it is safe and secure. It also keeps the systems that handle payments safe. It only lets the right people and computers use the programs that keep the retail business running. This is especially important when a lot of people are shopping, like on Black Friday. If something bad happens to a business on a day like that it does not just hurt the way people think of the business it also hurts the money the business makes and it happens right away minute by minute. Retail businesses, like these need Zero Trust to stay safe.
Healthcare
Healthcare organizations deal with private patient information and they need their systems to be working all the time. The Zero Trust approach makes sure that only people who have been verified and devices that meet the rules can get to records and systems.
This way Healthcare organizations can really cut down the risk of people getting into their systems and stealing patient data, which is what happens during ransomware attacks and data breaches. It also helps Healthcare organizations follow the rules that're in place to protect patient data.
Manufacturing & Industrial Systems
IoT devices, connected systems, and operational technology (OT) are essential components of contemporary manufacturing environments. Because of the laxer legacy security controls, these systems are frequently targeted.
In order to prevent attackers from moving laterally and interfering with operations, Zero Trust allows for secure segmentation between IT and OT environments. Additionally, it guarantees that only personnel and devices with permission can access vital production systems.
Technology, SaaS & Cloud-Native Enterprises
Rapid deployments and ongoing integration pipelines characterize the highly dynamic environments in which technology companies operate. Zero Trust integrates security throughout the entire development lifecycle, which is in line with DevSecOps.
It safeguards APIs, permits safe access to cloud security resources, and guarantees safe system and developer interaction without impeding innovation.
Education & Research Institutions
Educational institutions handle a lot of user data. At the same time, they want to be open and collaborative. This openness makes them a target for cyberattacks.
The Zero Trust approach helps to keep things secure while still being accessible.
It makes sure that students, faculty members and people from, outside who work together can only see the information they are supposed to see.
By doing this it lowers the risk of data leaks and people getting in who are not supposed to be. This way educational institutions can protect their data. Keep their environments open.
Government & Public Sector
Government organizations handle systems and private citizen information.
A Zero Trust approach helps protect access across departments. This means only people and devices that are verified can use government systems. It also helps make a country’s cyber defence stronger. This is done by reducing the chance of security breaches from happening. Government organizations and Zero Trust are key to keeping things secure.
Logistics & Supply Chain
Vendors, partners, and systems are all constantly communicating with one another in modern supply chains. They are extremely effective because of their degree of interconnectedness, but it also makes them vulnerable. A breach can spread throughout the entire ecosystem with just one weak link in the chain.
By ensuring that no vendor or outside partner is merely taken at their word, Zero Trust tackles this issue. Before any entity can touch anything, it must demonstrate its ownership, which keeps the supply chain functioning properly and greatly lowers the possibility of an outsider turning into the unexpected backdoor.
Energy & Utilities
Critical infrastructure that must always be operational is managed by energy and utility providers. By imposing stringent access controls and separating vital systems, Zero Trust safeguards these environments.
This reduces the possibility of cyberattacks that might interfere with vital services.
Telecommunications
Large-scale, dispersed networks with massive data flow are run by telecom companies. Infrastructure and customer data are shielded from unwanted access by Zero Trust, which guarantees secure access across network layers.
Business Benefits of Zero Trust Security
Zero Trust has actual, quantifiable benefits for companies in all sectors. Once an attacker gains access to a system, it limits the amount of damage that can be done when something goes wrong, which always happens. It's not necessary for a breach to turn into a disaster.
From an operational perspective, your teams will spend more time on work that truly matters and less time on manual approvals when access decisions are automated based on policy. There are fewer bottlenecks and things move more quickly.
Regulatory reviews are made much easier for compliance by Zero Trust’s ongoing monitoring and thorough audit trails. Organizations are ready for an audit rather than scrambling.
Customer trust, however, may be the greatest benefit and is not visible on a security dashboard. In a market where a single headline has the power to alter consumers’ perceptions of a brand, demonstrating your commitment to security is more than just a smart move. It gives you a competitive edge.
Learn more about building a resilient cybersecurity framework for enterprises in our related resource guide.
Zero Trust as a Business Strategy
Zero Trust is no longer just an IT initiative—it is a business strategy. Organizations that partner with experts like PIT Solutions for their Zero Trust implementation are better positioned to:
- Support remote and hybrid work environments
- Secure digital transformation initiatives
- Protect sensitive data across distributed systems
- Respond quickly to evolving cyber threats
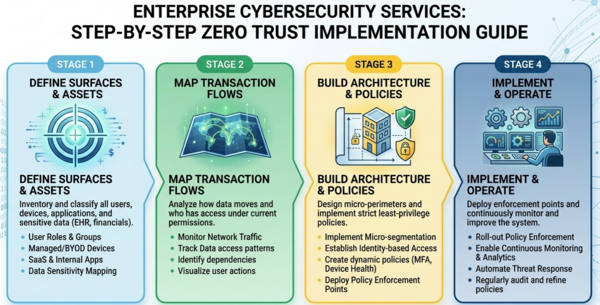
How to Implement Zero Trust Architecture
Knowing exactly who and what is accessing your systems and ensuring that every user and device is appropriately authenticated and authorized before they come into contact with vital resources are the first steps towards a successful Zero Trust implementation.
After that, the emphasis switches to establishing precise boundaries around delicate systems and ensuring that users only have access to what they truly require. On top of that, continuous monitoring keeps a close eye on system activity and user behavior in real time to make sure nothing goes unnoticed.
Rather than attempting a complete transformation at once, enterprises should adopt Zero Trust incrementally, starting with high-risk areas and expanding over time.
Future of Zero Trust Security
As cyber threats become more sophisticated, Zero Trust will continue to evolve with advancements in AI and automation. Future systems will be capable of making real-time, context-aware security decisions, enabling enterprises to stay ahead of threats without compromising user experience.
Conclusion: A Universal Security Model for Modern Enterprises
Zero Trust Architecture is a universal framework that applies across industries, addressing the shared challenges of modern enterprises.
By eliminating implicit trust and enforcing continuous verification, it enables organizations to operate securely in an increasingly complex digital environment.
For enterprises looking to strengthen their security posture while supporting business growth, Zero Trust is not just an option it is a necessity.
How PIT Solutions Supports Zero Trust Implementation
Implementing Zero Trust across an enterprise requires the right strategy, tools, and expertise.
PIT Solutions supports organizations across industries by:
- Assessing current security maturity
- Designing tailored Zero Trust architectures
- Integrating Zero Trust with cloud, DevSecOps, and enterprise systems
- Aligning implementations with compliance standards such as ISO 27001
If your organization is ready to adopt Zero Trust Architecture, PIT Solutions is here to guide you every step of the way from initial assessment to full Zero Trust implementation across your cybersecurity services stack. Don’t wait for a breach to act.

